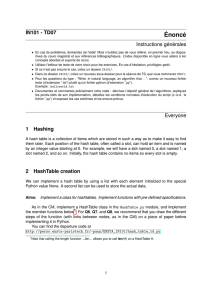
Algorithms II: Hash Tables & Python Implementation
Telechargé par
soufianelamrani2002

Algorithms II
PhD. Mohammed-Amine KOULALI
amine.k[email protected]
UM6P-CS
Mohammed VI Polytechnic University
13 maj 2022
1 / 43

Map as Python Dictionary
Lines 1–15 / 19
1import sys
f i l e n a m e = s y s . ar gv [ 1 ]
3
f r e q = {}
5for piece in open ( f i l e n a m e ) . r ea d ( ) . l ow er () . s p l i t ( ) :
# o nl y c o n s i d e r a l p h a b e t i c c h a r a c t e r s w i t h i n t h i s p i e c e
7word = ’ ’ . j o i n ( c for cin piece i f c . i s a l p h a ( ) )
i f word : # r e q u i r e a t ⤦
Çl e a s t one a l p h a b e t i c c h a r a c t e r
9f r e q [ word ] = 1 + f r e q . get ( word , 0 )
11 max_word = ’ ’
max_count = 0
13 for (w, c ) in f r e q . i t e m s ( ) : # ( key , v a l u e ) t u p l e s ⤦
Çr e p r e s e n t ( word , c o unt )
i f c > max_count :
15 max_word = w
4 / 43
 6
6
 7
7
 8
8
 9
9
 10
10
 11
11
 12
12
 13
13
 14
14
 15
15
 16
16
 17
17
 18
18
 19
19
 20
20
 21
21
 22
22
 23
23
 24
24
 25
25
 26
26
 27
27
 28
28
 29
29
 30
30
 31
31
 32
32
 33
33
 34
34
 35
35
 36
36
 37
37
 38
38
 39
39
 40
40
 41
41
 42
42
 43
43
 44
44
 45
45
 46
46
 47
47
 48
48
 49
49
 50
50
 51
51
 52
52
 53
53
 54
54
 55
55
 56
56
 57
57
1
/
57
100%