Implementing and
Operating Cisco
Security Core
Technologies (SCOR
350-701)
Version: Demo
[ Total Questions: 10]
Web: www.dumpscafe.com
Email: [email protected]
Cisco
350-701

IMPORTANT NOTICE
Feedback
We have developed quality product and state-of-art service to ensure our customers interest. If you have any
suggestions, please feel free to contact us at [email protected]
Support
If you have any questions about our product, please provide the following items:
exam code
screenshot of the question
login id/email
please contact us at and our technical experts will provide support within 24 hours.[email protected]
Copyright
The product of each order has its own encryption code, so you should use it independently. Any unauthorized
changes will inflict legal punishment. We reserve the right of final explanation for this statement.

Cisco - 350-701Pass Exam
2 of 7
Verified Solution - 100% Result
A.
B.
C.
D.
E.
A.
B.
C.
D.
Topic 3, Exam Pool C
Question #:1 - (Exam Topic 3)
What are two functions of IKEv1 but not IKEv2? (Choose two)
NAT-T is supported in IKEv1 but rot in IKEv2.
With IKEv1, when using aggressive mode, the initiator and responder identities are passed cleartext
With IKEv1, mode negotiates faster than main mode
IKEv1 uses EAP authentication
IKEv1 conversations are initiated by the IKE_SA_INIT message
Answer: C E
Question #:2 - (Exam Topic 3)
Which solution for remote workers enables protection, detection, and response on the endpoint against known
and unknown threats?
Cisco AMP for Endpoints
Cisco AnyConnect
Cisco Umbrella
Cisco Duo
Answer: A
Question #:3 - (Exam Topic 3)
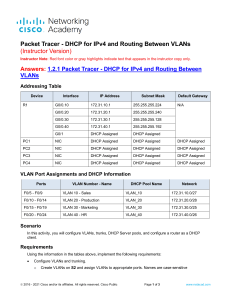
Refer to the exhibit.

Cisco - 350-701Pass Exam
3 of 7
Verified Solution - 100% Result
A.
B.
C.
D.
A.
B.
C.
D.
How does Cisco Umbrella manage traffic that is directed toward risky domains?
Traffic is proximed through the intelligent proxy.
Traffic is managed by the security settings and blocked.
Traffic is managed by the application settings, unhandled and allowed.
Traffic is allowed but logged.
Answer: B
Question #:4 - (Exam Topic 3)
Which API method and required attribute are used to add a device into Cisco DNA Center with the native
API?
GET and serialNumber
userSudiSerlalNos and deviceInfo
POST and name
lastSyncTime and pid
Answer: A
 6
6
 7
7
 8
8
 9
9
 10
10
1
/
10
100%